Your AI is Only as Smart as the Network Context You Give it
Ask an AI to help troubleshoot a voice quality complaint on your network. You’ll get an answer fast: check QoS policies, verify DSCP markings, review interface drops, and look at...
by NetBrain Feb 13, 2026
The combination of hybrid networks and manual network operations creates a high risk of service disruption due to the increased chance of human error and configuration drift. Closed-loop automation, from detection to verified remediation, offers a structured approach to managing rapid infrastructure changes. It follows a continuous sequence of detecting deviations, analyzing their causes, determining corrective action, verifying the outcome, and recording the process.
Each step of the process supports the next, replacing reactive troubleshooting and change management with a consistent, safe, and repeatable workflow. Below, we explore closed-loop automation technology and the guardrails that keep automated actions safe and controlled, detailing how these capabilities work together to support proactive, self-managing network operations.
Closed-loop automation is a continuous operational system that monitors the network, analyzes the findings with AI and automation, determines the corrective action, and verifies the outcome against the intended state. The loop stays active from the moment it detects an anomaly to verifications, replacing manual steps with a consistent process.
Many IT teams still use open-loop automation, which means the system can detect a problem but can’t adjust or correct anything on its own. Outdated solutions stop any action after sending an alert, leaving technicians to interpret the issue and decide how to resolve it. This creates delays and inconsistent outcomes where network conditions shift quickly.
Closed-loop automation reduces mean time to repair (MTTR) and prevents downtime by automating the entire incident response process. The system handles alerts or anomalies end-to-end: from diagnosis and prioritization to executing remediation via pre-approved processes. It applies the corrective steps identified during diagnosis using a library of change runbook templates and immediately checks the outcome through targeted validation tests. Once the results meet the expected state, the system continues to monitor and react to new conditions.
A closed-loop system progresses through defined steps, with each stage performing a distinct technical function. The automated workflow advances only when a stage produces the data or conditions required for the next, creating a controlled progression from initial detection to validation remediation. Each of these steps defines how automated workflows behave inside the complex infrastructure environments and establishes the sequence the system follows during every event.
The process starts with proactive monitoring of devices, service paths, traffic flows, and states and configurations. In hybrid environments, which encompass cloud computing, data centers, branches/campuses, and remote edges, conditions can shift rapidly, making this initial step necessary.
Detection systems monitor device telemetry, routing tables, logs, flow data, and test packets simulating real traffic to measure performance and path behavior. These solutions check for deviations from expected values, whether caused by congestion, device failure, configuration drift, or abnormal traffic distribution.
Data sources commonly used for detection include:
More recently, network automation has enabled proactive observability via continuous network assessments to check the live network (L2 and L3) for deviations from pre-defined golden configurations and states.
These signals trigger ITSM tickets and monitoring alerts and provide the remediation system with clear indications of failure points. Anomalies appear when observed values drift from baselines or policy thresholds, like:
High-fidelity detection filters out noise and focuses on conditions that affect performance, stability, or security.
Tickets and alerts trigger network automation to perform automatic diagnostics using AI, map the network incident, display contextual diagnosis results on the map for analysis, provide remediation steps for execution, assess the entire network for similar root causes, and monitor the network for the incident in the future.
By obtaining a deep understanding of the network through the creation of a live digital twin, an automation platform can monitor conditions across the hybrid network. This includes routing states, interface snapshots, logs, policy assignments, application paths and QoS, and configuration drift.
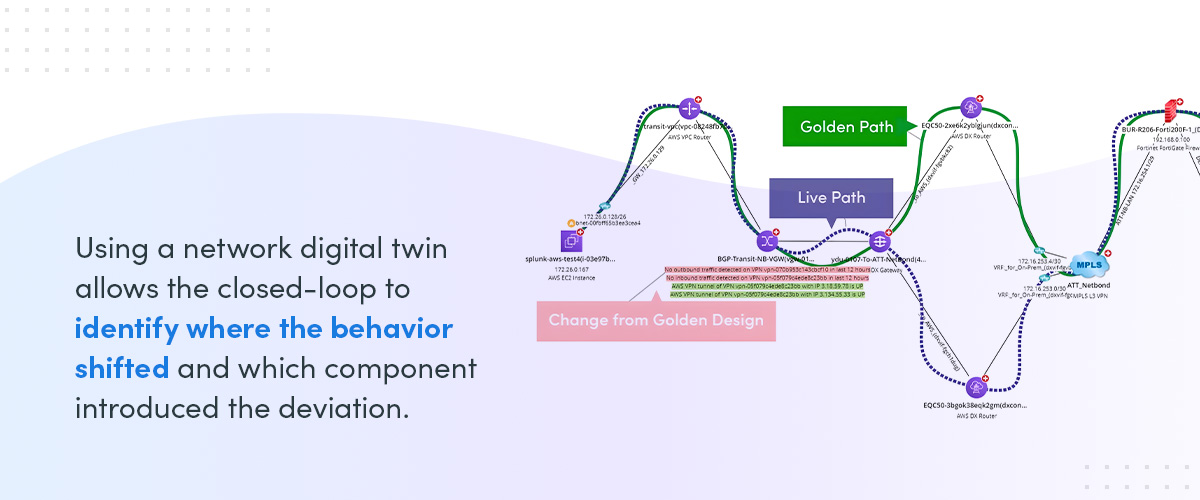
Using a network digital twin allows the closed-loop to identify where the behavior shifted and which component introduced the deviation. A network digital twin acts as a virtual model of the live environment, showing:
When an alert occurs, the auto-remediation system utilizes the collected telemetry, digital twin, and pre-built no-code automation as context to identify the root cause. Then, trained AI initiates diagnostic reasoning to determine the necessary automation to execute remediation, while noisy monitoring alerts can be automatically closed. Diagnostics can include:
These tests reduce the scope of the issue to a single device, link, configuration, or policy rules.
Change validation ensures the network is benchmarked against golden intents (states) and configurations before any action is taken. This includes verifying business requirements, adhering to architectural standards, and complying with security policies.
Validation tests whether the proposed fix aligns with expected capacity, segmentation rules, routing behavior, redundancy configurations, and access control boundaries during and after change execution.
Intent change validation includes reviewing the following:
Validation prevents changes that risk downtime caused by incorrect forwarding, policy violations, or unintended operational impact.
Execution applies the corrective action identified during root cause diagnosis and validated through intent checks. This stage uses AI-driven automation workflows to eliminate human error across devices and domains.
Workflows may be implemented as runbook automation or automation scripts. They contain the command sequence to apply, device targets, and required access, as well as pre-check verification steps.
Two execution models operate at this stage:
Automation handles repetitive tasks, such as updating route preferences, restoring policy entries, reapplying templates, or clearing transient faults. Human-over-the-loop workflows prepare a full technical context so the IT administrator can approve the change with complete visibility.
The execution relies on accurate data from the previous stages to make sure each action addresses the technical issue that was diagnosed.
Post-change validation confirms that the correction produced the intended state by comparing current conditions to the validated baseline without unintended consequences like downtime. It rechecks the infrastructure using the same intents used during detection and diagnosis. The verification stage stays active until the network matches the validated intent criteria.
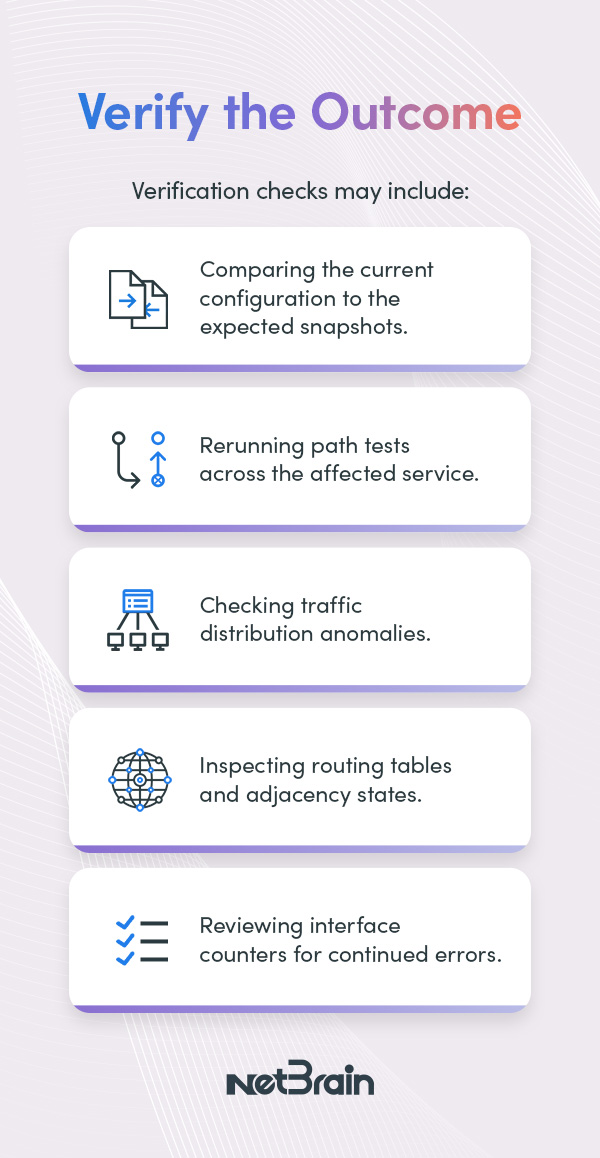
Verification checks may include:
Post-checks must run immediately to detect deviations early. If verification detects mismatches — like path asymmetry, new convergence delays, policy misalignment, or link errors — execution stops and triggers rollback procedures.
Logging documentation records every step taken during the closed-loop automation, from detection to verified remediation. If any unintended changes were made, it can roll back to any previous benchmarked state.
Logs capture all details associated with the automated workflow, including:
This documentation forms an immutable audit trail for root cause analysis (RCA), compliance reporting, and long-term trend analysis.
Closed-loop automation must operate within boundaries to preserve network stability and maintain control. In hybrid environments, interdependencies across devices, services, and domains mean that any automated remediation can affect multiple points and policies at once, so every action must follow defined constraints.
To keep this framework safe in production, the closed-loop is governed by safety controls. Each one manages a different aspect of operational risk and defines how it behaves in live environments. These safety controls include:
Safety guardrails define the operational perimeter for the remediation system. It sets the limits for where automated activity is permitted, which components it may modify, and what prerequisites must be satisfied before fixes can run. These controls prevent it from impacting infrastructure segments that can’t tolerate unintended adjustments.
Guardrails operate as explicit policy rules. They regulate execution across security zones, routing domains, application tiers, and multi-cloud boundaries. This structure is useful in hybrid systems where a single misapplied change can alter forward behavior or disrupt upstream dependencies.
Several types of guardrails determine how automation is allowed to operate:
Approval workflows introduce controlled decision points into the automated remediation system. They determine when automated actions proceed without intervention, with pre-approval, and when a human engineer must review the planned change.
In closed-loop systems, these gates are enforced via policy-as-code, with explicit preconditions, rollback criteria, and timeouts to prevent stalled or unsafe execution.
Each action is assigned a risk level before it is advanced. Classification is based on:
Risk scoring should rely on real dependency maps and modeled impact, not static labels. Inputs include topology, recent incident history, and whether the change touches shared services or control-plane state. The risk level determines the number of approval layers required.
Each tier maps to set guardrails that outline allowable action types, maximum affected nodes, and required evidence artifacts. Medium and high risk tiers often require simulation results or validation against the digital twin, along with a set rollback method if post-change validation fails.

Tiered models organize actions into these three levels of oversight:
The IT Service Management System (ITSM) provides the initial trigger needed to initiate an automated troubleshooting workflow. Network automation platforms can leverage AI to interpret incident tickets and determine which automation intents to use to diagnose the issue.
Auto-remediation systems can open or update change records, link configuration items (CIs) relationships, attach diagnostic outputs, and follow change advisory board (CAB) schedules, blackout periods, and emergency change procedures. This ensures that automated changes are governed by the same operational and compliance requirements as traditional workflows.
Roles define who may authorize each category of action. This prevents unauthorized execution and assigns responsibility to the correct engineering team member.
Role binding should be granular and enforced through identity and access management (IAM) and role-based access control (RBAC) with least-privilege scopes. Escalation paths and on-call substitutions must be codified to prevent approval deadlocks.
Audit logging records every approval and ties it to the automated workflow. Logs must be immutable and linked to the run ID, the proposed changes, test artifacts, and final device commits.
This supports post-incident reconstruction, compliance requirements, and model retraining by connecting each approval to its outcome. Each approval record includes:
Automated rollback restores the infrastructure to a known and validated state when a corrective action produces an unexpected condition, activating as soon as verification is detected from the intended outcome.
The rollback process includes:
Closed-loop automation relies on a structured framework to detect issues, diagnose root causes, validate intents, apply fixes, verify outcomes, and record steps. Implementing this framework manually can be difficult across hybrid environments with constant change.
NetBrain’s automation platform delivers these capabilities natively through its live Digital Twin, Continuous Assessment, and AI-Assisted Runbook Automation, providing data, context, and workflows needed to support each stage of the closed loop.
Ready to move from a reactive to a proactive network operations model? Discover how NetBrain’s AI-powered Automation network operations can help you implement a safe and effective closed-loop automation strategy. Request your personalized demo today to see it in action.
Ask an AI to help troubleshoot a voice quality complaint on your network. You’ll get an answer fast: check QoS policies, verify DSCP markings, review interface drops, and look at...
For customers evaluating how to expand network operations beyond legacy configuration management, NetBrain is now officially recognized in the Infoblox Ecosystem as a Certified Partner for Infoblox NIOS integration. This...
Modern network environments don’t live in a single system. Network teams operate in real time. Hardware and facilities teams manage physical infrastructure. Platform and operations teams need dashboards they can trust without giving every...
We use cookies to personalize content and understand your use of the website in order to improve user experience. By using our website you consent to all cookies in accordance with our privacy policy.